Worldwide Network of Information Transmission and Processing in Military
A globally networked, end-to-end collection of information capabilities for on-demand to warfighters, policymakers, and supporting all the defense forces.
Metaverse: 3D Virtual Environment of The Internet
Metaverse will provide you with a hyper-real alternate universe in which you can exist real and virtual reality at the same time. However, it has its own set of drawbacks and advantages, Learn more...
RAT: Control of a Machine Over a Remote Network Connection
Remote Access Trojans can Control a Machine Over a Remote Network Connection and collect massive amounts of data from infected machines. Learn more about how to be safe.
Hyperreality: The Fusion of Physical and Virtual Worlds
We are living in a world where our experiences are mediated by technology, where simulations and representations are taking over the real. Learn more about the concept of hyperreality.
Nanotechnology in Future Warfare and Defense
The growth of Nanotechnology in Future Warfare and Defence has a dominant platform at the forefront of military interests in the use, or misuse of its power.
Nanotechnology: Manipulating Atoms and Molecules
Nanotechnology is the science of building small, really really small; it's pretty difficult to imagine how small it is. It has major benefits as well as Potential risks too. Learn more
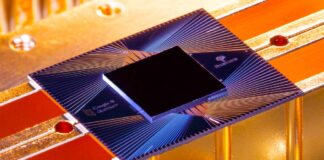
Quantum Computing: A New Frontier in Technology
Learn how Quantum Computing is considered a new frontier in technology, with the potential to transform a wide range of industries and fields.
Guerrilla Warfare: The Unconventional Method of War
In this article learn, what is Guerrilla Warfare, its Origin, Strategies and Objectives, and Some of the well-known Guerilla Wars in History.
Artificial City: The Future of Artificially Intelligence Society
Explore the concept of an Artificial City and its potential implications, benefits, drawbacks, challenges, and The Future of an Artificially Intelligence Society.
Virtual Worlds: The Next Frontier in Technology
In this article, we will explore the different aspects of virtual worlds, including their history, technology, and impact on society.
Dyson Sphere: a hypothetical megastructure and a thought experiment.
Dyson sphere A hypothetical megastructure and hypothetical technology that allows us to discover advanced civilizations elsewhere in this vast galaxy.
Network-Centric Warfare: A New War Theory Emerging in the Information Age
A new war theory in the Information Age known as Network-centric warfare, represents the military's response to the Information Age. Learn what is network-centric warfare?