Nanotechnology: Manipulating Atoms and Molecules
Nanotechnology is the science of building small, really really small; it's pretty difficult to imagine how small it is. It has major benefits as well as Potential risks too. Learn more
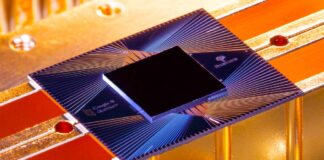
Quantum Computing: A New Frontier in Technology
Learn how Quantum Computing is considered a new frontier in technology, with the potential to transform a wide range of industries and fields.
Hyperreality: The Fusion of Physical and Virtual Worlds
We are living in a world where our experiences are mediated by technology, where simulations and representations are taking over the real. Learn more about the concept of hyperreality.
Invisible War in Orbit: Are GPS Disruptions a Sign of Secret...
GPS failures, drifting ships, and mid-air navigation loss, are global powers fighting a hidden war in space? The truth may already be unfolding above us.
Data Democratization: Empowering the Masses with Information Access
This article explores the concept of data democratization, its benefits and challenges, and its impact on various sectors of society.
Network-Centric Warfare: A New War Theory Emerging in the Information Age
A new war theory in the Information Age known as Network-centric warfare, represents the military's response to the Information Age. Learn what is network-centric warfare?
Chemical Warfare: Intentional Use of Toxins in Warfare
Explore the nature of chemical warfare, its historical context, devastating consequences and the international efforts to combat its use.
Mars in 30 Days? Why Faster Rockets Won’t Solve Human Spaceflight
Buzzwords like “Mars in 30 Days” make great headlines, and recent prototype claims from Rosatom and other propulsion projects have reignited the hype; however,...
Dyson Sphere: a hypothetical megastructure and a thought experiment.
Dyson sphere A hypothetical megastructure and hypothetical technology that allows us to discover advanced civilizations elsewhere in this vast galaxy.
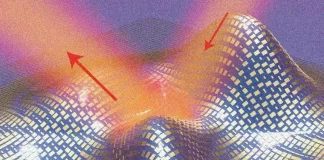
Metamaterials and the Science of Invisibility
Explore what are metamaterials, its properties, and applications, including the science of invisibility.
Directed Energy Weapons: Evolving Technology of the Modern Warfare
Laser weapons once thought to be science fiction now becoming true. Learn what Directed energy weapons are and the potential they hold for the future of warfare and defense.
Virtual Worlds: The Next Frontier in Technology
In this article, we will explore the different aspects of virtual worlds, including their history, technology, and impact on society.