Biological Warfare: Emerging Weapons of Mass Destruction
Biological warfare, germ warfare, or the use of biological toxins; it's an Emerging Weapons of Mass Destruction in the 21st century. Learn more how
Worldwide Network of Information Transmission and Processing in Military
A globally networked, end-to-end collection of information capabilities for on-demand to warfighters, policymakers, and supporting all the defense forces.
Classified AI on Secret Networks: How Militaries Are Quietly Building the...
Nations are quietly integrating AI into secure military networks. Here’s how the next AI arms race is unfolding worldwide.
Data Democratization: Empowering the Masses with Information Access
This article explores the concept of data democratization, its benefits and challenges, and its impact on various sectors of society.
Geoengineering: Prevention from Climate Change or Unknown Climate Risk
Geoengineering is an intentional intervention in the Earth's natural processes to prevent the effects of climate change. But is it Prevention from Climate Change or Unknown Climate Risk?
AI Surveillance Secrets: The Government Files Still Classified in 2026
AI surveillance is expanding worldwide but the laws, data sources, and algorithms behind it remain classified. Inside the files governments won’t release in 2026.
Metaverse: 3D Virtual Environment of The Internet
Metaverse will provide you with a hyper-real alternate universe in which you can exist real and virtual reality at the same time. However, it has its own set of drawbacks and advantages, Learn more...
Black body Radiation: The Thermal Electromagnetic Radiation
Learn about Black Body Radiation, an idealized physical body that absorbs all incident electromagnetic radiation, regardless of frequency or angle of incidence. History of this theory and the Application of black body radiation.
Electronic Warfare: The Digital Battlefield in Modern Warfare
In this article learn the intricacies of electronic warfare, explore its various components, including tactics, and implications for modern warfare with FAQs.
Weather Warfare: Weather Modification Technology in Warfare
The Hazardous Nature of the Environment has attracted it to be modified as a weapon of war. Know how it can be used in Weather Warfare.
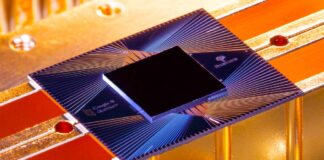
Quantum Computing: A New Frontier in Technology
Learn how Quantum Computing is considered a new frontier in technology, with the potential to transform a wide range of industries and fields.
Psychotronic Torture: Mind Control Using Electromagnetic Radiation
Implanting sounds and ideas into people's minds, and using them as a Psychotronic weapon to kill and do the actions the controller wants. Learn what Psychotronic Torture is.