Hyper-Automation: Concept of Automating Everything in an Organization
The next level beyond regular automation is called hyper-automation. In this article learn what is hyper-automation. Different technologies, devices or platforms, its advantages and disadvantages in this article.
Nanotechnology in Future Warfare and Defense
The growth of Nanotechnology in Future Warfare and Defence has a dominant platform at the forefront of military interests in the use, or misuse of its power.
Quantum Networks: The Future of Secure Communication and Computing
Quantum Networks, In this article, we will explore what quantum networks are, how they work, and their potential applications.
Guerrilla Warfare: The Unconventional Method of War
In this article learn, what is Guerrilla Warfare, its Origin, Strategies and Objectives, and Some of the well-known Guerilla Wars in History.
AI Surveillance Secrets: The Government Files Still Classified in 2026
AI surveillance is expanding worldwide but the laws, data sources, and algorithms behind it remain classified. Inside the files governments won’t release in 2026.
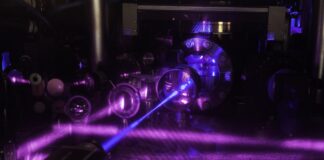
Exploring the Science Behind Quantum Key Distribution
Science Behind Quantum Key Distribution. In this article, we will explore the basics of QKD, how it works, and its applications.
Muons: Unstable Subatomic Particle
Know about Muon an unstable sub-atomic particle. Why we call it an unstable subatomic particle? why it's average lifetime is 2.2 μs?
Metamaterials and the Science of Invisibility
Explore what are metamaterials, its properties, and applications, including the science of invisibility.
Quantum Cryptography: Data Security at the Quantum Level
Based on Heisenberg’s Uncertainty Principle and Quantum Entanglement Quantum Mechanical Properties to Perform Cryptographic Tasks What is this Quantum Cryptography?
Metaverse: 3D Virtual Environment of The Internet
Metaverse will provide you with a hyper-real alternate universe in which you can exist real and virtual reality at the same time. However, it has its own set of drawbacks and advantages, Learn more...
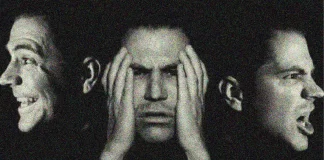
Psychotronic Torture: Mind Control Using Electromagnetic Radiation
Implanting sounds and ideas into people's minds, and using them as a Psychotronic weapon to kill and do the actions the controller wants. Learn what Psychotronic Torture is.
Quantum Information Science: Information Science with Quantum Effects in Physics
Quantum Information Science is a new field of science and technology that integrates physical science, mathematics, computer science, and engineering. Learn more